That thread does not exist.
Forum
News
What We Know About Israel's Missile Attack on Iran

Man sets himself on fire outside Trump trial in horrific scene as onlookers watch wild blaze

Emergency rooms refused to treat pregnant women, leaving one to miscarry in a lobby restroom
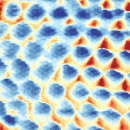
Quantum Crystal of Frozen Electrons - the Wigner Crystal - is Visualized for the First Time

Governor Sanders Declares State of Emergency Ahead of Eclipse

Marjorie Taylor Greene Thinks The Solar Eclipse Is God Telling Us Something

Google to Delete Billions of Browsing Records in 'Incognito Mode' Privacy Lawsuit Settlement